SharePoint WSP Repackage
A few years ago I wrote an article explaining how to manually modify a SharePoint WSP solution using a specific software, over the years I got feedback about adware being added to the computers during the installation process of the software.
I recently tried to install this particular software and my antivirus automatically pop up saying that the file was not safe, to get rid of all this issues I decided to build a specific application to repackage all the files inside of the WSP solution.
A WSP is nothing more than a CAB file that contains a few XML files linking the resources that will be copied to SharePoint.
CAB files can be easily open with a zip tool like 7zip but the majority of the software’s do not compress files in the CAB format.
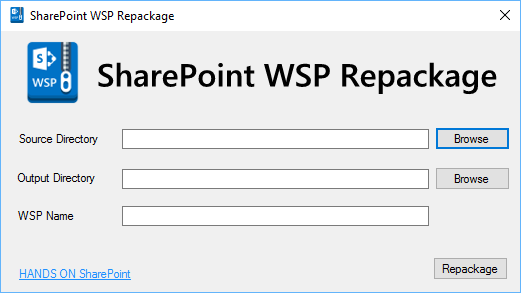
The WSP Repackage is really easy to use, just need to select the folder where all the WSP files are located, select the output directory and provide the name to the WSP file in a matter of seconds the compressed WSP solution will be ready.
In the first version the WSP Repackage only compress the files, if you want to add or remove files to the solution make sure that you reference them in the XML files otherwise they might be ignored when you deploy the solution or cause an error.
A tool like this is useful in scenarios where you need to edit a solution or webpart and you don’t have access to the Visual Studio project.
The source code is available on github and codeplex and you are welcomed to contribute with new ideas and with new versions of this tool.
I have plans to make it more efficient, in the next version I’ll implement a validation that will check if all the files are referenced in the xml files and also if all the referenced files still exist in the solution.
Feel free to comment and give me your suggestions to the product.

 HANDS ON tek
HANDS ON tek
 M365 Admin
M365 Admin



November 15, 2016
Greetings joao,
Nice little utility here… but after scanning it with various anti-virus tools prior to installing it on my own laptop, even your little utility is generating several alerts from my AV software…
In other words, you’ve ended up TRIGGERING the very sort of problem your utility was meant to AVOID 😐 .
I’ll still test-drive your utility – AFTER I hear back from Avast that one of your key files is doesn’t contain any malware.
Just thought you’d want to know…
It’s actually HARD to do a good deed these days, don’t you think? 😉
Cheers,
-Mark
December 27, 2016
Hi Mark,
All the code is available on git hub you can download the source and compile it with visual studio if you want to.
I think this days all exe files are automatically triggered as problematic files.
Let me know if you got a reply from Avast.
Cheers,
João Ferreira